I’m still amazed Veeam and it’s partners squeezed in 85 break out sessions throughout the event. I had a tough decision most of the time on which session to attend as many sessions shared the same time slot. Fortunately, the schedule listed details for each session saying if it was business, partner, or technical. Then technical had a few levels so that helped to describe how deep the session will go.
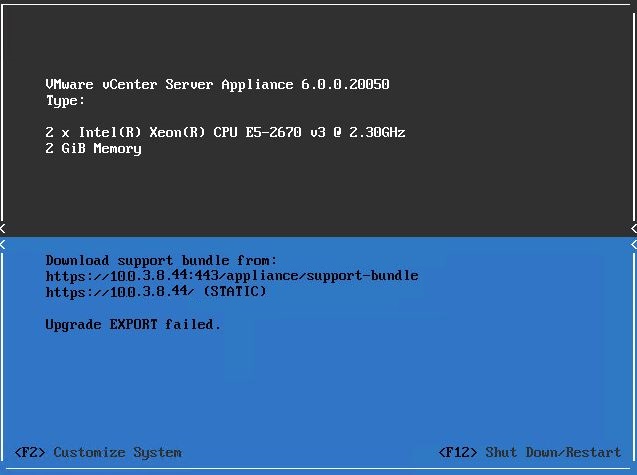
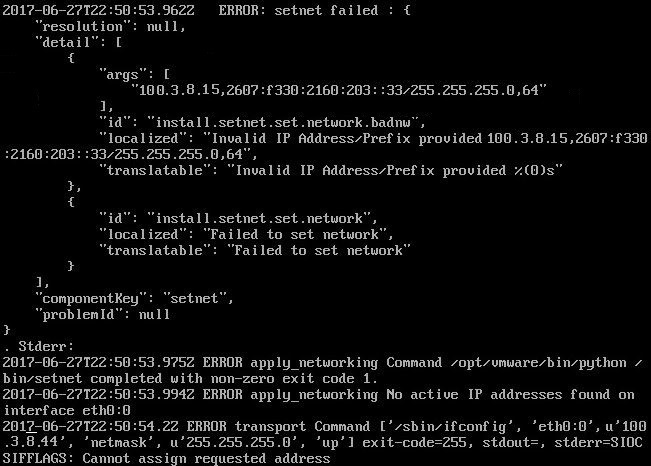
My favorite session was How to Back Up and Restore VMware vCenter Server Appliance (vCSA) and Platform Controllers Properly. The session was hosted by a Emad Younis, Technical Marketing Engineer from VMware, and Mike White, Technical Evangelist from Veeam Software. They started off talking about VMware Platform Services Controller. The PSC was new to vSphere 6 so it’s been around for a little while now, but good to get a refresher. Then they went into backing up and restoring the vCSA and PSC. Backing up the vCSA in 6 is the same as previous versions. Do not bother backing up the vCSA’s databases. Use Veeam or another product to back up the vCSA and PSC VMs. Then restore the vCSA VM directly to a host. However, the PSC is a little different if using Enhanced Linked Mode, which means there will be more than one PSC. Deploy a new PSC and join to the existing SSO domain. Replication will simply kick in and bring the PSC up to speed. If only one PSC, then just restore it.
I thought there would have been more love for Veeam ONE. There were actually only two sessions! I know it’s the sidekick to Back and Replication, but more sessions on it would have been appreciated. I attended one of the two. The second one wasn’t relevant to me since it was about how to scale Veeam ONE. My Veeam ONE server is fine. The session I attended, Take Out the Guesswork with Veeam ONE & Chargeback, went into some reports and alarms. A couple of the reports, powered off VMs and VMS with no archive copy are ones that I never looked. There are a great many of reports so nice to get some tips on others to look at outside of my routine ones. They talked about a useful tip on creating an alarm for a VM that has not be backed up for defined amount of time. This is good to catch a bug that sometime stops backing up VMs within a vApp with no warning or error.
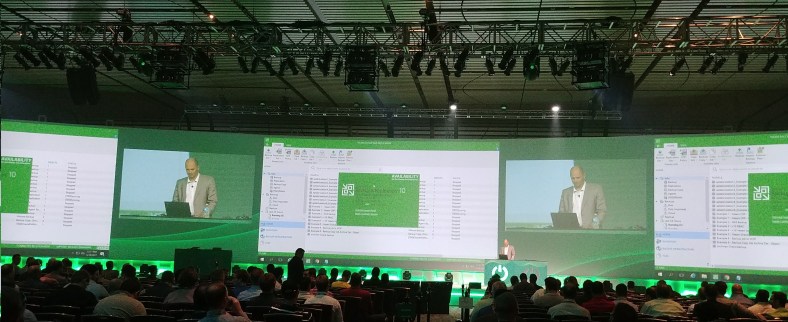
The photo above was from What’s New in v10: A Deeper Dive, hosted by Anton Gostev. His sessions seemed to be the most popular by far. People were lining up for his sessions that were in the smaller rooms, but at least the deep dive was in the big hall.
The breakout sessions were hit and miss as some of the presenters did a better job than others with going through their topics. However, I certainly understand that every presenter puts in a lot of time and effort. I got something out of each session I went to. Perhaps one day I can think of an interesting topic to present and start small at a local VMUG.